Introducción
La metodología de desarrollo SecDevOps, que integra los principios de seguridad (Security), desarrollo (Development) y operaciones (Operations), ha surgido como una respuesta a los desafíos actuales en la creación y gestión de software. Este enfoque busca incorporar la seguridad de manera temprana y continua en todas las fases del ciclo de vida del desarrollo, permitiendo la entrega ágil y sostenida de aplicaciones robustas y seguras. SecDevOps responde tanto a la necesidad de eficiencia y rapidez en el desarrollo como a la protección de datos, la prevención de vulnerabilidades y la capacidad de respuesta ante amenazas emergentes.
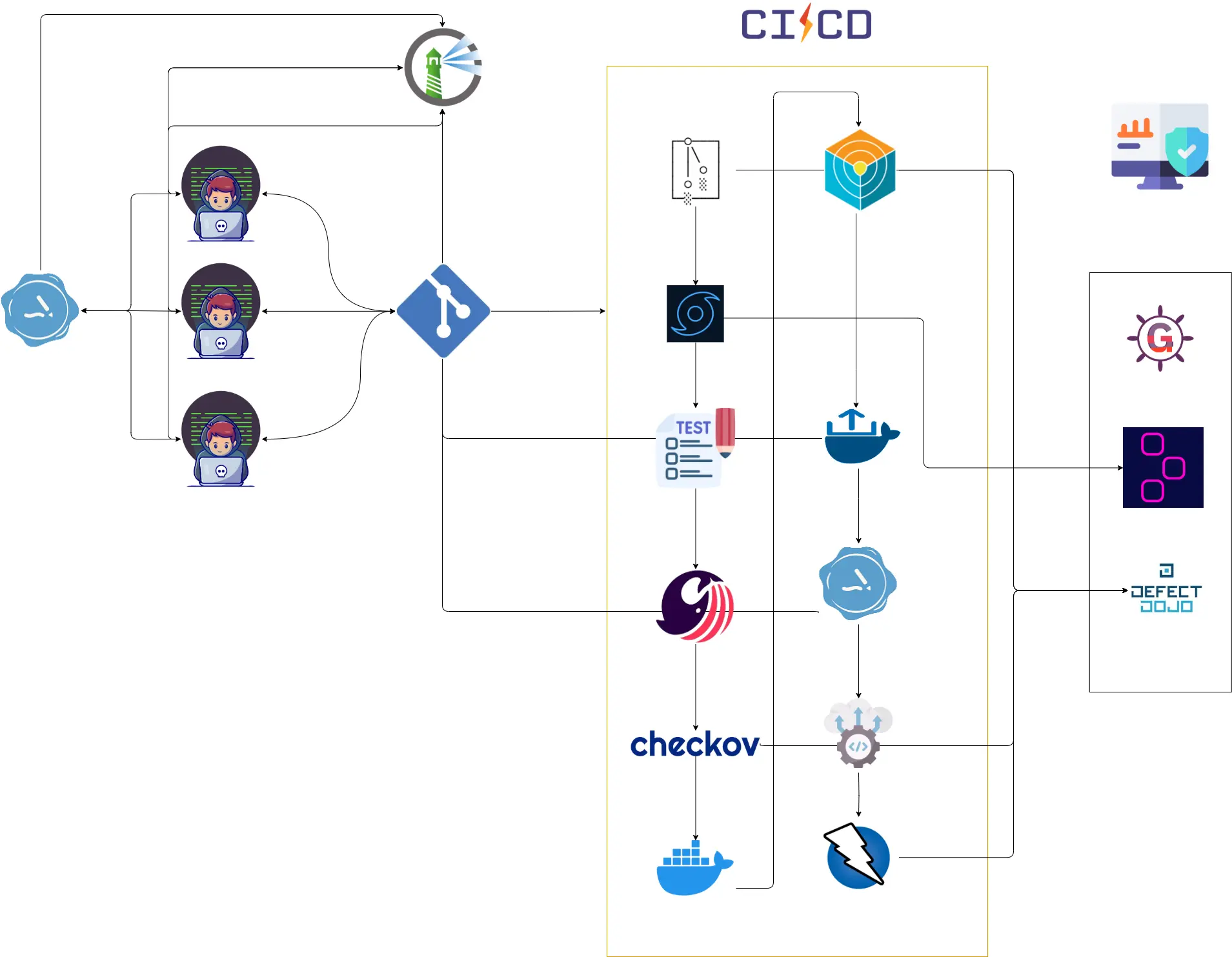
Con este objetivo, se ha creado el marco de trabajo Open SecDevOps (OSDO), orientado a facilitar la integración de la seguridad en los procesos de desarrollo mediante el uso de herramientas de código abierto, buenas prácticas y automatización.
La metodología SecDevOps se fundamenta en la colaboración estrecha entre los equipos de desarrollo, operaciones y seguridad, promoviendo una cultura organizacional donde la seguridad es una responsabilidad compartida. A través de ciclos iterativos e incrementales, SecDevOps fomenta la mejora continua y la adaptación a nuevos retos tecnológicos y de negocio. Los componentes clave de su funcionamiento incluyen:
Integración continua de la seguridad:
SecDevOps promueve la incorporación de controles y prácticas de seguridad desde las etapas iniciales del diseño hasta la puesta en producción. Esto implica la revisión de requisitos de seguridad, el análisis de riesgos, la definición de políticas y la aplicación de estándares de codificación segura. Los equipos colaboran para identificar y mitigar riesgos y vulnerabilidades de forma proactiva.
Automatización y pruebas continuas:
La automatización es un pilar fundamental en SecDevOps. Se emplean herramientas para la ejecución automática de pruebas de seguridad, tanto estáticas (SAST) como dinámicas (DAST), análisis de dependencias (SCA), escaneo de contenedores y validación de configuraciones. Estas pruebas se integran en los pipelines de CI/CD, permitiendo la detección temprana y la corrección eficiente de problemas de seguridad antes de que lleguen a producción.
Despliegue continuo y monitorización:
La entrega continua facilita la implementación frecuente y controlada de cambios en el software, minimizando el riesgo de errores y vulnerabilidades. La monitorización constante de aplicaciones, infraestructuras y servicios permite detectar comportamientos anómalos, incidentes de seguridad y posibles ataques en tiempo real. Además, se promueve la recolección y análisis de métricas para la mejora continua y la respuesta rápida ante incidentes.
Gestión de la configuración y cumplimiento:
SecDevOps incluye la gestión automatizada de configuraciones seguras y la verificación del cumplimiento de normativas y estándares de seguridad. Esto abarca la gestión de secretos, la aplicación de parches, la revisión de permisos y la auditoría de cambios en los sistemas.
Cultura y formación en seguridad:
La adopción de SecDevOps implica la sensibilización y capacitación continua de todos los miembros del equipo en materia de seguridad. Se fomenta la comunicación abierta, la colaboración interdisciplinar y la responsabilidad compartida para mantener altos niveles de seguridad en todo el ciclo de vida del software.
En conjunto, SecDevOps y el marco OSDO proporcionan una base sólida para el desarrollo de aplicaciones seguras, resilientes y alineadas con las necesidades actuales de las organizaciones, facilitando la adaptación a un entorno tecnológico en constante evolución.